Articles

CVE-2026-28426: Chain Reaction Stored XSS and Antlers Template Injection in Statamic Control Panel
—
by
Summary CVE-2026-28426 describes a critical stored cross-site scripting vulnerability in Statamic CMS control panel that…

Thousands of Public Google Cloud API Keys Exposed as Live Gemini Access Tokens: Risks and Remediation
—
by
Overview New security research from Truffle Security found nearly 3,000 Google Cloud API keys with…

Hacker News for macOS: A Native SwiftUI Client Built for Power Readers
—
by
Overview Hacker News for macOS is a native macOS client built with SwiftUI that delivers…

How to Fix Microsoft Teams Error: We Couldn’t Connect the Call
—
by
We couldn’t connect the call is a common Microsoft Teams error that appears when a…

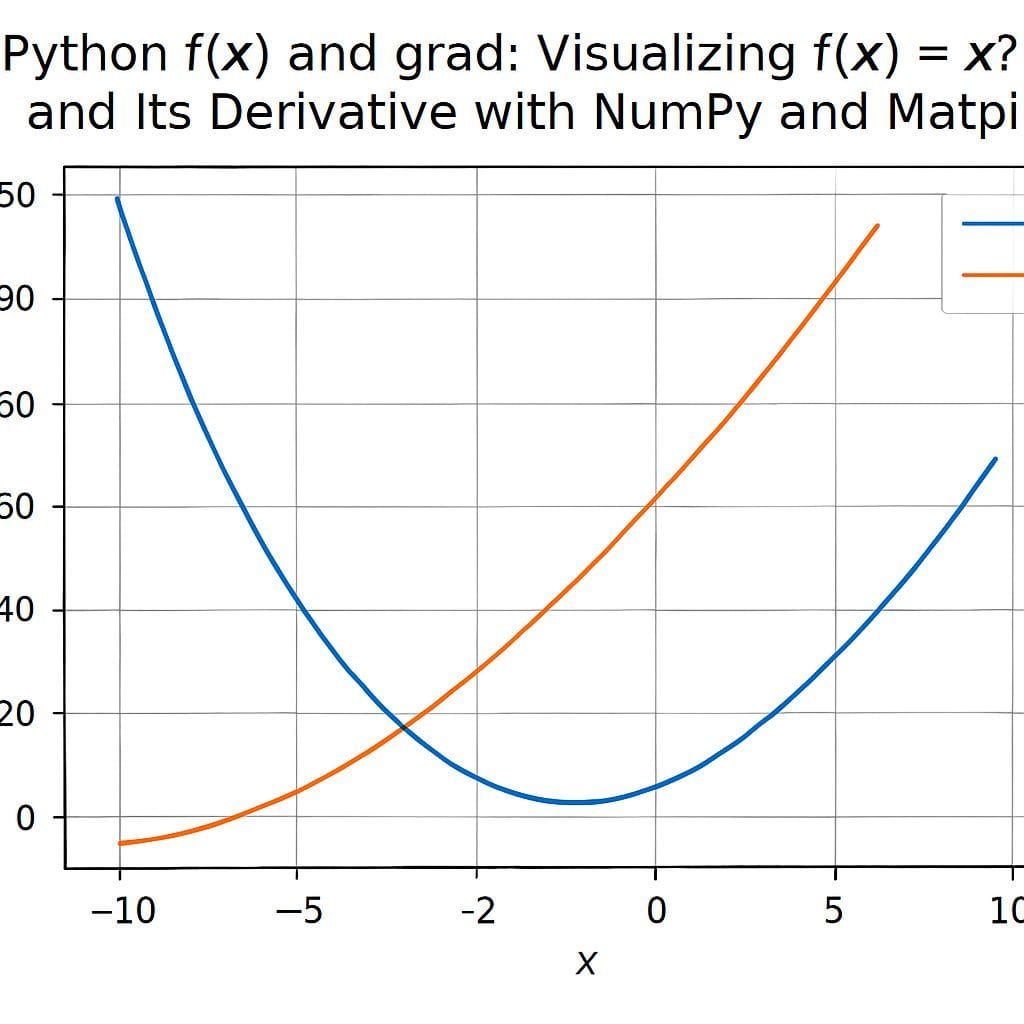
Python f(x) and grad: Visualizing f(x)=x^2+20 and Its Derivative with NumPy and Matplotlib
—
by
Introduction This article explains how to compute and visualize a simple scalar function f(x) =…

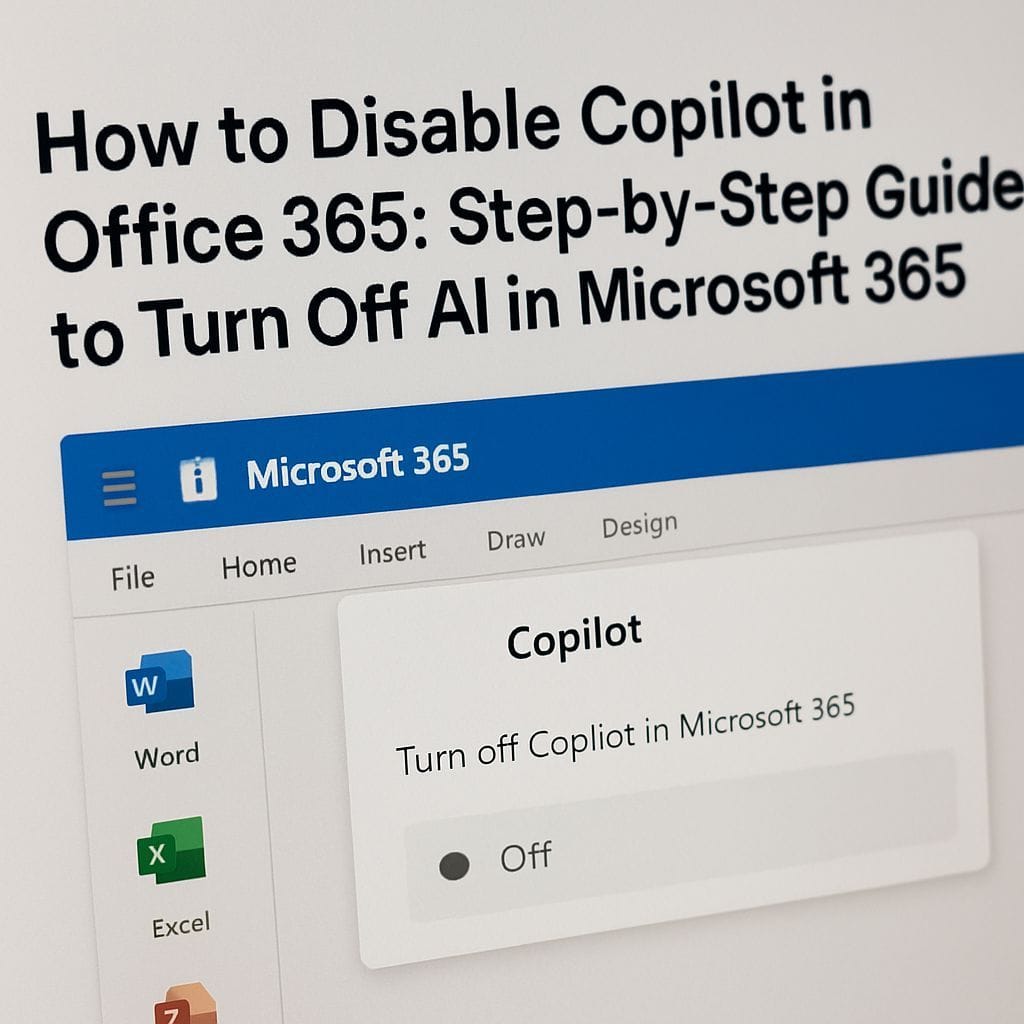
How to Disable Copilot in Office 365: Step-by-Step Guide to Turn Off AI in Microsoft 365
—
by
Introduction Many Office 365 and Microsoft 365 users are asking how to disable Copilot and…

How to Fix App Notifications in Windows: Step-by-Step Guide for Windows 10 and Windows 11
—
by
Are app notifications delayed, missing, or silent in Windows? You are not alone. Many Windows…

Do LLMs Lie? Why Large Language Models Sound Smart While Making Things Up
—
by
Introduction: The Illusion of Confidence You ask a large language model a question and get…

Using an Old Device? 5 Account Security Settings You Should Enable Now
—
by
Introduction Keeping an older phone, tablet, or laptop in service is common when upgrading is…

Beginner-Friendly Guide: LeetCode 1404 Binary String Reduction (C++, Python, JavaScript)
—
by
Summary: This guide explains how to solve LeetCode problem 1404, where you must count the…